Send With Confidence
Partner with the email service trusted by developers and marketers for time-savings, scalability, and delivery expertise.


Time to read: 9 minutes
Email marketing is full of obscure acronyms that can be confusing to understand—and DMARC is no exception.
Domain-based Message Authentication, Reporting & Conformance or DMARC is an email security measure that protects your domain against hacker attacks. We’ll explain DMARC here and how it’ll help you control email deliverability and protect your brand reputation. Still with us? Let’s dive in.
DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It's an email authentication protocol that adds an extra layer of security to the email verification process to combat email spoofing.
DMARC is designed to give email domain owners the ability to protect their domain from unauthorized use, commonly known as email spoofing. Email spoofing is a tactic used in phishing attacks and other cyber threats, where the attacker disguises an email to make it appear as if it's coming from a legitimate source. This is done to deceive recipients into disclosing personal information, downloading malware, or engaging in other actions that can lead to security breaches.
DMARC uses other standard authentication protocols—like Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM)—to help administrators catch emails sent by cyberattackers that impersonate a legitimate organization. This practice is spoofing and is possible because the attacking email’s "from" address appears identical to a legitimate domain.
SPF (Sender Policy Framework) allows domain owners to specify which email servers are permitted to send email on behalf of their domain. When an email is received, the receiving email server checks the SPF record to verify that the email comes from an authorized server.
DKIM (DomainKeys Identified Mail) involves adding a digital signature to outgoing emails. This signature is validated against a public key in the domain's DNS records, confirming that the email content hasn't been tampered with during transit.
DMARC ties SPF and DKIM together by allowing domain owners to specify a policy in their DNS records that dictates how receiving email servers should handle emails that fail SPF and DKIM checks. DMARC also provides a mechanism for reporting back to the domain owner about emails that pass or fail these checks, giving insights into potential authentication issues or spoofing attempts.
DMARC enables email senders to specify how to handle emails authenticated using SPF or DKIM. These senders can then opt to send those emails to the junk folder or block them altogether.
In doing so, internet service providers (ISPs) can more effectively identify spammers and prevent malicious emails from landing in consumer inboxes. DMARC also allows ISPs to minimize false positives and provide better authentication reporting—vastly improving transparency in the marketplace.
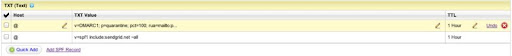
Your DMARC record appears alongside your Domain Name System (DNS) records’:
It’s also crucial to note that not all receiving servers will perform a DMARC check before accepting a message, but all the major ISPs do—and implementation of DMARC checks continues to grow. Learn more about the ins and outs of DMARC.
There are 4 main reasons you'd want your DNS server administrator to add your DMARC record and start monitoring your domain:
You can inspect what a DMARC record looks like by typing “< dig txt _dmarc.sendgrid.net >” into your terminal. Then, check Valimail to view the DMARC record for any domain that has one published.
Here’s an example of Twilio SendGrid’s DMARC record:
v=DMARC1;p=none;rua=mailto:dmarc@sendgrid.com;ruf=mailto:dmarc@sendgrid.com;rf=afrf;pct=100
If you’ve ever had phishing problems in the past or own a financial business that processes sensitive information (or any business for that matter), enabling DMARC authentication can be a valuable tool. In fact, there’s no disadvantage to implementing a DMARC policy now as a way to preempt future email authentication issues due to cyberattackers.
You should also keep in mind that DMARC aggregate and forensic reports are machine-readable, so it can be difficult for humans to make sense of them. As such, you’ll need to use a DMARC report-monitoring service like Valimail—a SendGrid partner—that can collect the reports and access the information.
Once you’ve decided whether to implement DMARC and have selected the services you want enabled, there are 5 steps to follow to set up DMARC:
Start by completing the sender authentication process for your account. Doing so ensures that emails sent through your SendGrid account will be properly signed using DKIM and SPF for your unique domain.
If you need help completing this step, read our documentation for help.
Send yourself a handful of test emails to confirm everything works correctly. Then, verify that the DKIM and SPF signatures in your email headers match the domain you’re using to allowlist your SendGrid account.

Create a TXT resource record that email receivers can use to determine your DMARC preferences within your DNS registrar. You can accomplish this task within the domain host’s DNS registrar, which is likely in the same location where you created the records for the sender authentication—at the domain’s root level, not the subdomain.
Keep in mind that an unqualified email sent to and received from a DMARC-participating recipient result in their email client doing the following:
These reports will contain information that can help you evaluate which services send mail on behalf of your domain.
Here’s a sample report containing only one record that shows the results for 2 emails.
<report_metadata>
<org_name>receiver.com
noreply-dmarc-support@receiver.com
<extra_contact_info>http://receiver.com/dmarc/support
<report_id>9391651994964116463
<date_range>
1335571200
1335657599
<policy_published> sender.com
r
r
none
none
100
<source_ip>72.150.241.94
2 <policy_evaluated> none
fail
pass
<header_from>sender.com
<auth_results>
sender.com
fail
<human_result>
sender.net
pass
<human_result>
sender.com
pass
(Note: The listed SPF and DKIM auth_results are raw results, regardless of the “s=” alignment. The file name appears as “filename = receiver “!” policy-domain “!” begin-timestamp “!” end-timestamp “.” extension” (e.g., receiver.org!sender.com!1335571200!1335657599.zip).
Also, keep in mind that aggregate reports get sent as a .zip attachment, so be sure the address you define can accept attachments in this file type.
Now that you’ve tested and tweaked your mail streams to determine who sends email on behalf of your domain, it’s time to turn it up a notch.
Until now, you should have only used the “p=none” policy to get reports of any bad behavior to learn the email origination. Now, it’s time to adjust your DMARC record’s policy to begin controlling how receivers handle mail claiming to be from your domain.
DMARC records are crucial to the evolution of sophisticated email authentication. Plus, these serve as excellent case studies for the importance of email senders and ISPs working together to maximize the security of their email channel.
Visit the DMARC organization’s website to learn more about this valuable authentication protocol. Then, discover how to authenticate your email with Twilio SendGrid in just 5 simple steps.
Ready to start sending? Sign up for a free Twilio SendGrid account (no credit card required) and send 100 emails per day on a Free Forever account.
Partner with the email service trusted by developers and marketers for time-savings, scalability, and delivery expertise.